The Open Door
Objective
| Difficulty | Description |
|---|---|
| 1/5 | Help Goose Barry near the pond identify which identity has been granted excessive Owner permissions at the subscription level, violating the principle of least privilege. |
Goose Lucas mission statement
(Spanish mode) Hi… welcome to the Dosis Neighborhood! Nice to meet you!
Please make sure the towns Azure network is secured properly.
The Neighborhood HOA uses Azure for their IT infrastructure.
Audit their network security configuration to ensure production systems aren’t exposed to internet attacks.
They claim all systems are properly protected, but you need to verify there are no overly permissive NSG rules.
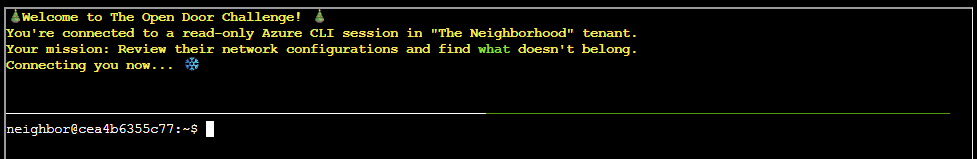
The Open Door Terminal
This objective focuses on reviewing cloud network security controls to identify overly permissive access. By inspecting Azure network security group (NSG) rules, the task highlights how misconfigured inbound rules can unintentionally expose production systems to the internet, undermining basic network segmentation and perimeter defenses.
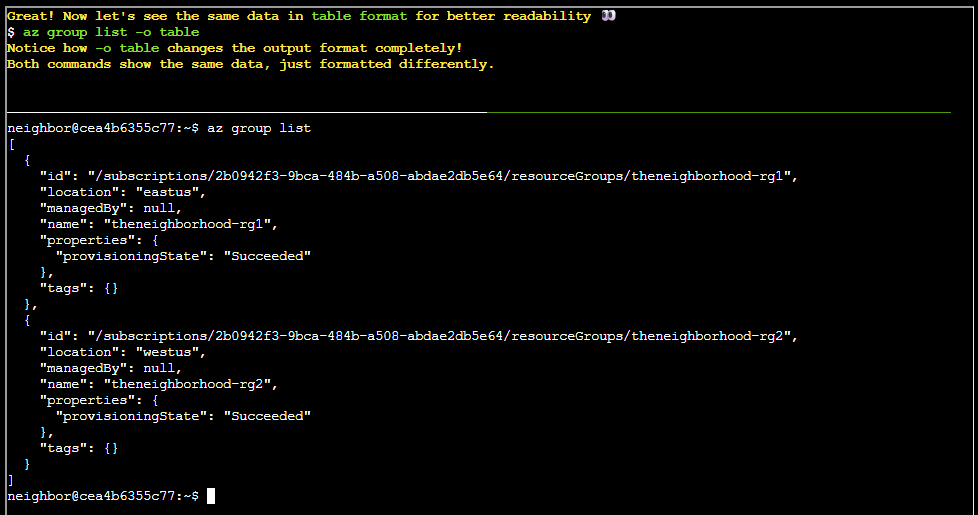
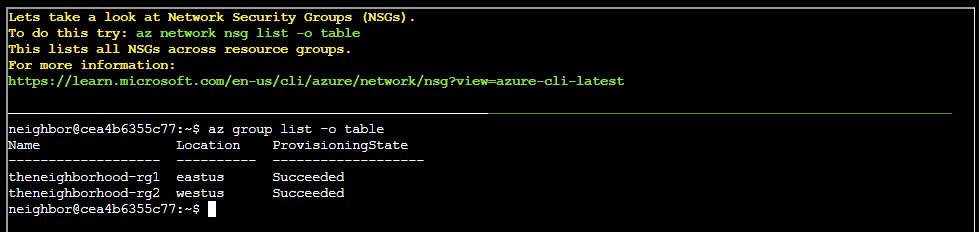
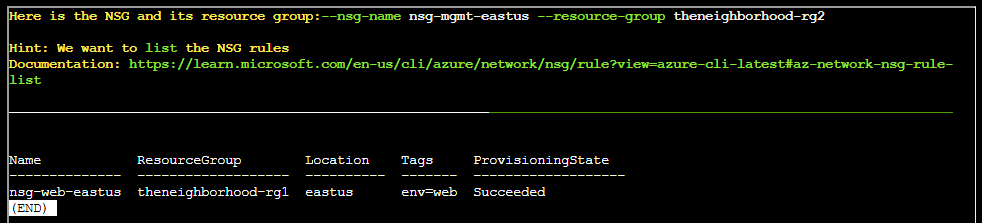
az group listaz group list -o tableaz network nsg list -o table| Location | Name | ResourceGroup |
|---|---|---|
| eastus | nsg-web-eastus | theneighborhood-rg1 |
| eastus | nsg-db-eastus | theneighborhood-rg1 |
| eastus | nsg-dev-eastus | theneighborhood-rg2 |
| eastus | nsg-mgmt-eastus | theneighborhood-rg2 |
| eastus | nsg-production-eastus | theneighborhood-rg1 |
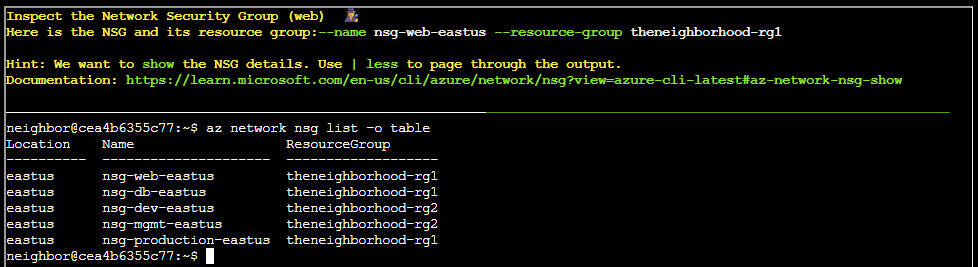
az network nsg show -o table --name nsg-web-eastus --resource-group theneighborhood-rg1az network nsg rule list --name nsg-mgmt-eastus --resource-group theneighborhood-rg2 | lessViewing suspect rules
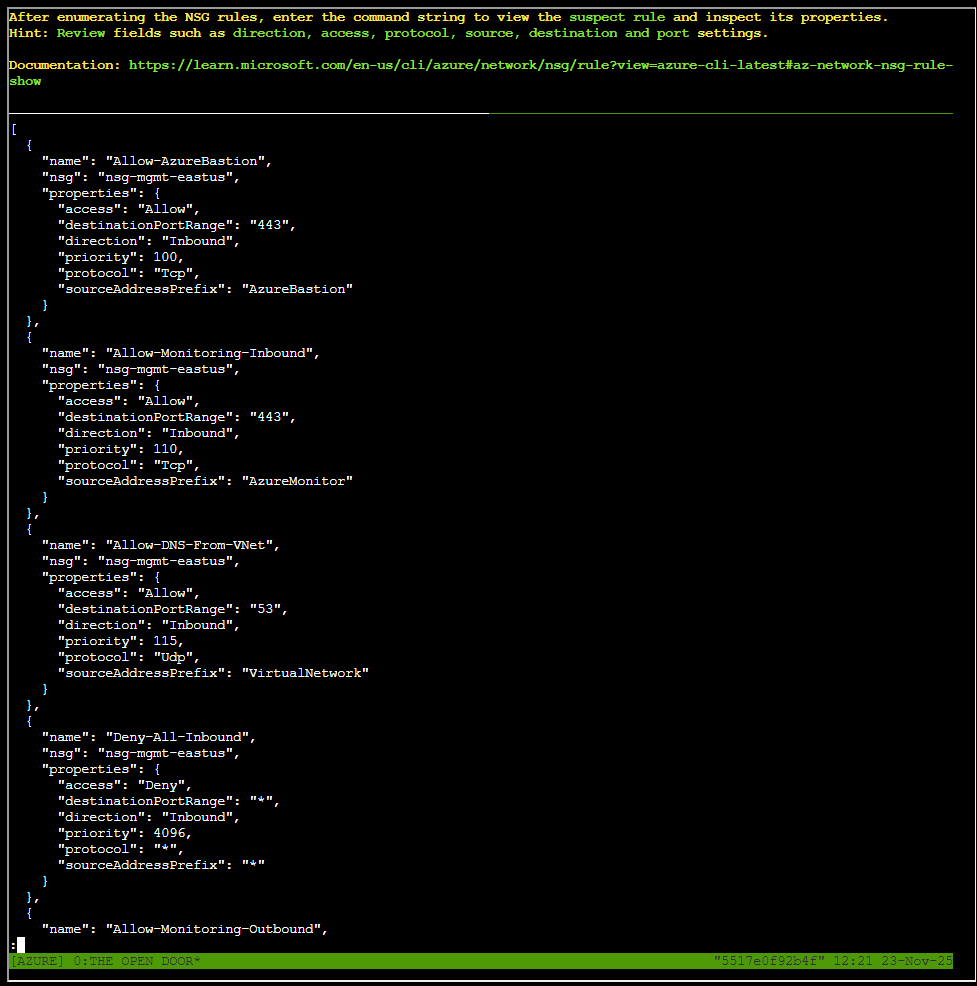
Rules theneighborhood-rg2 _ nsg-mgmt-eastus
az network nsg rule list --name nsg-mgmt-eastus --resource-group theneighborhood-rg2 | lessRules for resource group “theneighborhood-rg2” and NSG name “nsg-mgmt-eastus”
- Allow-AzureBastion
- Allow-Monitoring-Inbound
- Allow-DNS-From-VNet
- Deny-All-Inbound
- Allow-Monitoring-Outbound
- Allow-AD-Identity-Outbound
- Allow-Backup-Outbound
Inspecting the each rule by the followign command:
az network nsg rule show --nsg-name nsg-mgmt-eastus --resource-group theneighborhood-rg2 -n <rulename>None of these yielded something interesting.
Rules theneighborhood-rg2 _ nsg-dev-eastus
az network nsg rule list --name nsg-dev-eastus --resource-group theneighborhood-rg2 | lessRules for resource group “theneighborhood-rg2” and NSG name “nsg-dev-eastus”
- Allow-HTTP-Inbound
- Allow-HTTPS-Inbound
- Allow-DevOps-Agents
- Allow-Jumpbox-Remote-Access
- Deny-All-Inbound
Inspecting the each rule by the followign command:
az network nsg rule show --nsg-name nsg-dev-eastus --resource-group theneighborhood-rg2 -n <rulename>None of these yielded something interesting.
Rules theneighborhood-rg1 _ nsg-web-eastus
az network nsg rule list --name nsg-web-eastus --resource-group theneighborhood-rg1 | lessRules for resource group “theneighborhood-rg1” and NSG name “nsg-web-eastus”
- Allow-HTTP-Inbound
- Allow-HTTPS-Inbound
- Allow-AppGateway-HealthProbes
- Allow-Web-To-App
- Deny-All-Inbound
Inspecting the each rule by the followign command:
az network nsg rule show --nsg-name nsg-web-eastus --resource-group theneighborhood-rg1 -n <rulename>None of these yielded something interesting.
Rules theneighborhood-rg1 _ nsg-db-eastus
az network nsg rule list --name nsg-db-eastus --resource-group theneighborhood-rg1 | lessRules for resource group “theneighborhood-rg1” and NSG name “nsg-db-eastus”
- Allow-App-To-DB
- Allow-AD-Trusted-Subnet
- Deny-All-Inbound
Inspecting the each rule by the followign command:
az network nsg rule show --nsg-name nsg-db-eastus --resource-group theneighborhood-rg1 -n <rulename>None of these yielded something interesting.
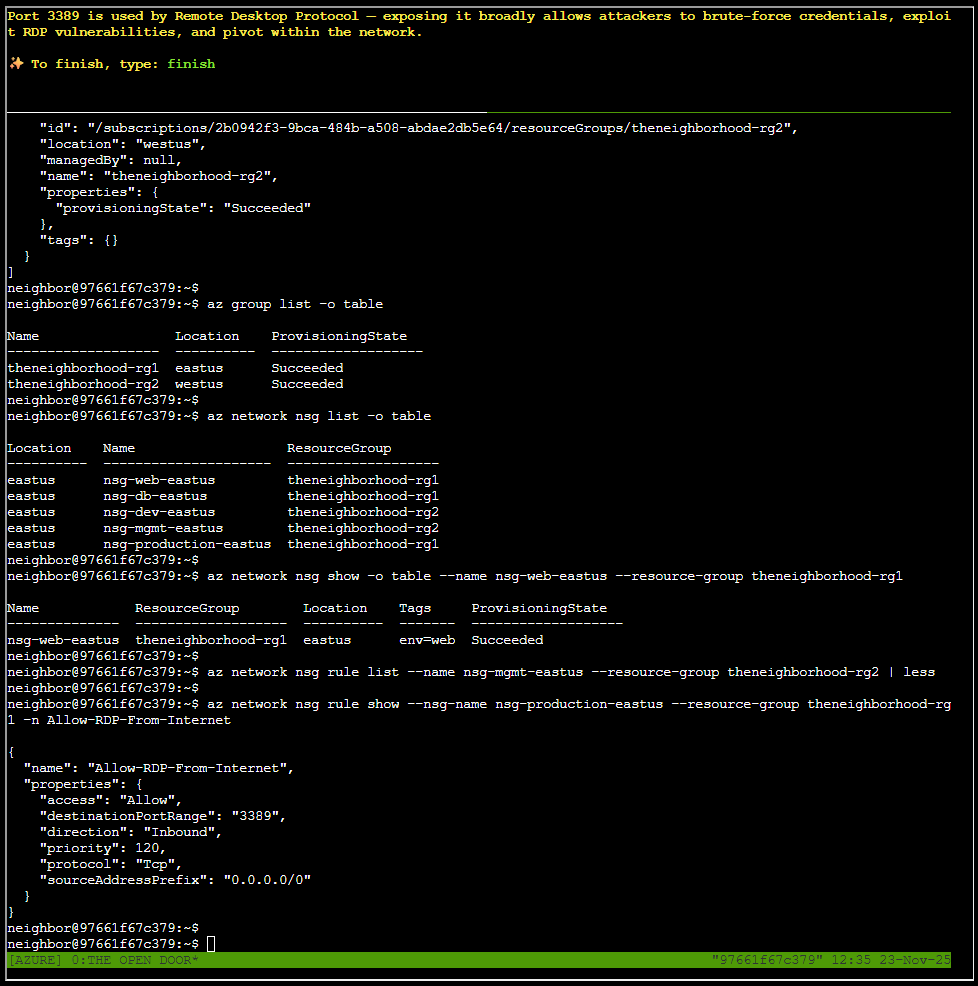
Rules theneighborhood-rg1 _ nsg-production-eastus
az network nsg rule list --name nsg-production-eastus --resource-group theneighborhood-rg1 | lessRules for resource group “theneighborhood-rg1” and NSG name “nsg-production-eastus”
- Allow-HTTP-Inbound
- Allow-HTTPS-Inbound
- Allow-AppGateway-HealthProbes
- Allow-RDP-From-Internet
- Deny-All-Inbound
Inspecting the each rule by the followign command:
az network nsg rule show --nsg-name nsg-production-eastus --resource-group theneighborhood-rg1 -n <rulename>As I were traversing and inspecting these rules, I caught one of interest. A RDP related one:
az network nsg rule show --nsg-name nsg-production-eastus --resource-group theneighborhood-rg1 -n Allow-RDP-From-InternetGoose Lucas closing words
After solving, Lucas says:
Ha! ‘Properly protected’ they said. More like ‘properly exposed to the entire internet’! Good catch, amigo.