About Roger Johnsen
Roger Johnsen is an information security professional with a strong focus on Blue Team operations, threat hunting, and detection engineering. His work centers on strengthening SOC capabilities through hypothesis-driven hunting, analyst education, and the development of tooling and processes that scale beyond individual investigations.
Roger is an active participant in Capture The Flag (CTF) competitions, with particular emphasis on technically demanding, long-form challenges such as the SANS Holiday Hack Challenge and platforms like TryHackMe and Hack The Box. He approaches CTFs as controlled environments for validating techniques, stress-testing assumptions, and refining investigative workflows that directly translate into real-world security operations.
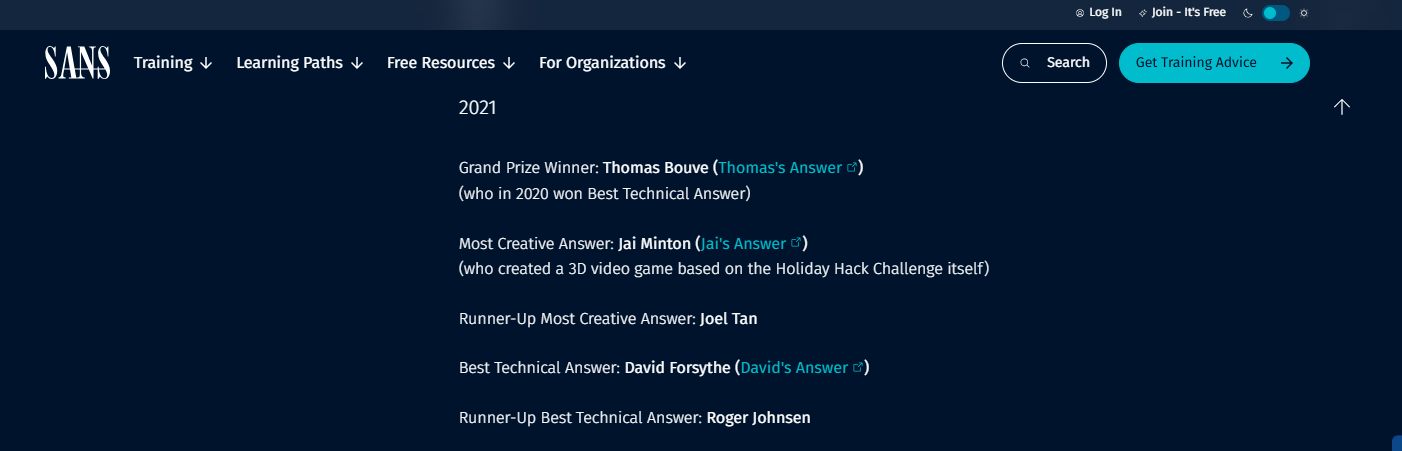
In the SANS Holiday Hack Challenge 2021, Roger was recognized as runner-up for Best Technical Answer, earning a challenge coin for the depth, clarity, and technical rigor of his submission. He has consistently ranked near the top in subsequent editions, narrowly missing first place — a pattern that continues to fuel his yearly participation.
With a background in systems development, programming, and security operations, Roger emphasizes technical correctness, reproducibility, and quality over shortcuts or surface-level solutions.
Predefender
Predefender, founded by Roger Johnsen, is a professional initiative focused on advancing practical, high-quality threat hunting.
Its primary resource, the Predefender Threat Hunt Book, functions as both a reference and a living knowledge base for SOC analysts and Blue Team practitioners. The material combines Threat-Informed Defense, MITRE ATT&CK, and the Lockheed Martin Kill Chain with real investigative workflows, emphasizing documentation, reasoning, and reproducibility.
Predefender deliberately bridges detection engineering and programming, reflecting the belief that effective threat hunting requires more than tooling alone. The goal is not only to detect malicious activity, but to understand adversary behavior well enough to continuously improve defenses.